There is a story about a man whose life turned into a living hell. After the man made a video of him and his girlfriend having sex, he uploaded it on Facebook in order to keep it and enjoy watching it by his own. However, after he mistakenly posted the video publically instead of privately, the clip went viral, spreading throughout the Internet. Soon after, his friends saw the video as it continued to spread at an astonishing rate through Social Network Service and Person-to-Person(P2P) services.
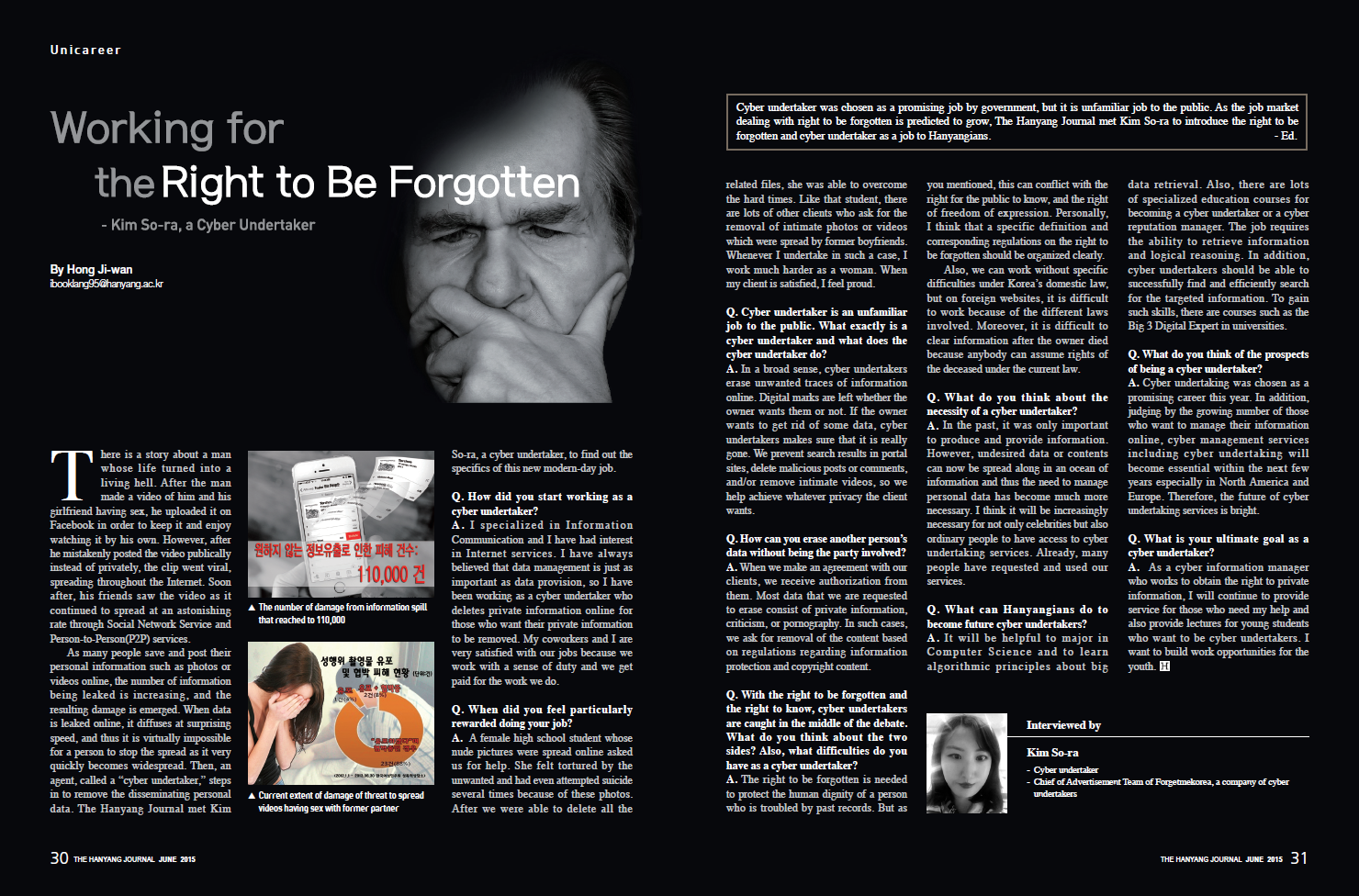
As many people save and post their personal information such as photos or videos online, the number of information being leaked is increasing, and the resulting damage is emerged. When data is leaked online, it diffuses at surprising speed, and thus it is virtually impossible for a person to stop the spread as it very quickly becomes widespread. Then, an agent, called a “cyber undertaker,” steps in to remove the disseminating personal data. The Hanyang Journal met Kim So-ra, a cyber undertaker, to find out the specifics of this new modern-day job.
Q. How did you start working as a cyber undertaker?
A. I specialized in Information Communication and I have had interest in Internet services. I have always believed that data management is just as important as data provision, so I have been working as a cyber undertaker who deletes private information online for those who want their private information to be removed. My coworkers and I are very satisfied with our jobs because we work with a sense of duty and we get paid for the work we do.
Q. When did you feel particularly rewarded doing your job?
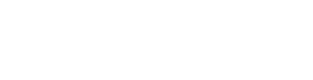
A. A female high school student whose nude pictures were spread online asked us for help. She felt tortured by the unwanted and had even attempted suicide several times because of these photos. After we were able to delete all the related files, she was able to overcome the hard times. Like that student, there are lots of other clients who ask for the removal of intimate photos or videos which were spread by former boyfriends. Whenever I undertake in such a case, I work much harder as a woman. When my client is satisfied, I feel proud.
Q. Cyber undertaker is an unfamiliar job to the public. What exactly is a cyber undertaker and what does the cyber undertaker do?
A. In a broad sense, cyber undertakers erase unwanted traces of information online. Digital marks are left whether the owner wants them or not. If the owner wants to get rid of some data, cyber undertakers makes sure that it is really gone. We prevent search results in portal sites, delete malicious posts or comments, and/or remove intimate videos, so we help achieve whatever privacy the client wants.
Q. How can you erase another person’s data without being the party involved?
A. When we make an agreement with our clients, we receive authorization from them. Most data that we are requested to erase consist of private information, criticism, or pornography. In such cases, we ask for removal of the content based on regulations regarding information protection and copyright content.
Q. With the right to be forgotten and the right to know, cyber undertakers are caught in the middle of the debate. What do you think about the two sides? Also, what difficulties do you have as a cyber undertaker?
A. The right to be forgotten is needed to protect the human dignity of a person who is troubled by past records. But as you mentioned, this can conflict with the right for the public to know, and the right of freedom of expression. Personally, I think that a specific definition and corresponding regulations on the right to be forgotten should be organized clearly. Also, we can work without specific difficulties under Korea’s domestic law, but on foreign websites, it is difficult to work because of the different laws involved. Moreover, it is difficult to clear information after the owner died because anybody can assume rights of the deceased under the current law.
Q. What do you think about the necessity of a cyber undertaker?
A. In the past, it was only important to produce and provide information. However, undesired data or contents can now be spread along in an ocean of information and thus the need to manage personal data has become much more necessary. I think it will be increasingly necessary for not only celebrities but also ordinary people to have access to cyber undertaking services. Already, many people have requested and used our services.
Q. What can Hanyangians do to become future cyber undertakers?
A. It will be helpful to major in Computer Science and to learn algorithmic principles about big data retrieval. Also, there are lots of specialized education courses for becoming a cyber undertaker or a cyber reputation manager. The job requires the ability to retrieve information and logical reasoning. In addition, cyber undertakers should be able to successfully find and efficiently search for the targeted information. To gain such skills, there are courses such as the Big 3 Digital Expert in universities.
Q. What do you think of the prospects of being a cyber undertaker?
A. Cyber undertaking was chosen as a promising career this year. In addition, judging by the growing number of those who want to manage their information online, cyber management services including cyber undertaking will become essential within the next few years especially in North America and Europe. Therefore, the future of cyber undertaking services is bright. Q. What is your ultimate goal as a cyber undertaker? A. As a cyber information manager who works to obtain the right to private information, I will continue to provide service for those who need my help and also provide lectures for young students who want to be cyber undertakers. I want to build work opportunities for the youth.